A flaw in a popular smart plug allows hackers to execute remote code, potentially putting businesses and homes at risk of attack, according to a recent McAfee report.
Smart plugs are Wi-Fi-connected electric outlets that give users the ability to remotely turn lights and appliances on and off, and monitor them online. But the Wemo Insight Smart Plug, produced by Belkin, included an unreported buffer overflow in the libUPnPHndlr.so library, known as flaw CVE-2018-6692.
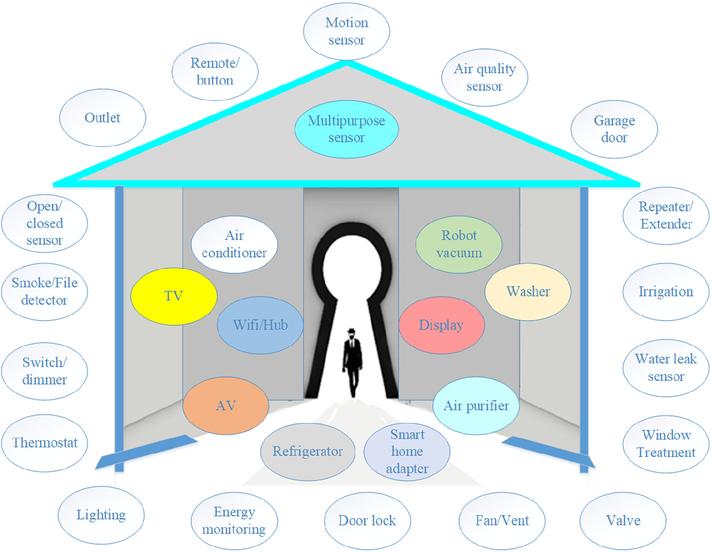
While the smart plug itself may not be very useful to attackers, like other Internet of Things (IoT) devices, if it is networked with others, the threat level grows. The plug could act as an entry point into the network to launch other attacks, the report noted.
SEE: Internet of Things policy (Tech Pro Research)
The researchers discovered two attack techniques that can be used to exploit this vulnerability: A write-what-where, and overwriting the return address on the stack. These allowed them to gain complete control of the device.
McAfee reported their findings to Belkin in May, the report said.
This flaw discovery underlines the importance of manufacturers using secure coding practices when making connected devices, the report noted. If the Wemo plugs were used in conference rooms or offices, they could have posed a major issue for those businesses.
“IoT devices are frequently overlooked from a security perspective; this may be because many are used for seemingly innocuous purposes such as simple home automation,” the report said. “However, these devices run operating systems and require just as much protection as desktop computers. A vulnerability such as we discovered could become the foothold an attacker needs to enter and compromise an entire business network.”
SEE: Internet of Things (IoT): Cheat sheet (TechRepublic)
This also serves as a reminder to perform due diligence when it comes to purchasing secure IoT devices, and to properly secure those devices with strong passwords and other measures after purchasing them to keep your home and business networks safe.
For more tips on how to create secure IoT devices, click here. And for tips on how to secure the IoT devices you already have, click here.









